- Table of Contents
- 1. Introduction
- 2. Understanding Cloud Storage
- 3. Current Security Risks in2025
- 4. Vulnerabilities in Cloud Storage
- 5. Best Practices for Secure Cloud Storage
- 5.1 Encryption
- 5.2 Authentication
- 5.3 Compliance with Privacy Laws
- 5.4 Malware Protection
- 5.5 Threat Prevention
- 6. Step-by-Step Instructions for Securing Cloud Storage
- Step 1: Assess Your Requirements
- Step 2: Choose a Secure Cloud Provider
- Step 3: Implement Strong Authentication Practices
- Step 4: Encrypt Data
- Step 5: Regularly Audit Access and Permissions
- Step 6: Monitor for Threats
- Step 7: Develop a Backup Strategy
- Step 8: Educate Employees
- 7. Case Studies
- 8. Expert Insights
- Expert Opinion: Dr. Jane Doe, Cybersecurity Researcher
- Expert Opinion: John Smith, Cloud Security Consultant
- 9. Conclusion
As organizations continue to migrate to cloud storage solutions, securing sensitive data has become increasingly critical. The landscape of cybersecurity is constantly evolving, and with it, the methods employed by cybercriminals. This guide aims to provide a comprehensive understanding of the state of secure cloud storage in 2025, covering the latest security risks, vulnerabilities, best practices, and expert insights to help organizations strengthen their security posture.
Table of Contents
- Introduction
- Understanding Cloud Storage
- 2.1 What Is Cloud Storage?
- 2.2 Types of Cloud Storage
- Current Security Risks in 2025
- 3.1 Data Breaches
- 3.2 Ransomware Attacks
- 3.3 Insider Threats
- 3.4 Misconfiguration
- Vulnerabilities in Cloud Storage
- Best Practices for Secure Cloud Storage
- 5.1 Encryption
- 5.2 Authentication
- 5.3 Compliance with Privacy Laws
- 5.4 Malware Protection
- 5.5 Threat Prevention
- Step-by-Step Instructions for Securing Cloud Storage
- Case Studies
- Expert Insights
- Conclusion
1. Introduction
In 2025, the adoption of cloud storage solutions has become ubiquitous across industries. With this shift, understanding the nuances of cybersecurity in the cloud is essential. From protecting sensitive data to ensuring compliance with regulations, organizations must navigate an intricate landscape fraught with risks. This guide will equip you with the knowledge needed to secure cloud storage effectively.
2. Understanding Cloud Storage
2.1 What Is Cloud Storage?
Cloud storage allows users to store data on remote servers rather than on local machines. This service is usually hosted by cloud service providers (CSPs) and enables easy access and sharing of files from any location with internet connectivity.
2.2 Types of Cloud Storage
-
Public Cloud: Services offered over the public internet and shared among multiple clients (e.g., AWS, Google Drive).
-
Private Cloud: Exclusive cloud environments for a single organization, offering greater control and security.
-
Hybrid Cloud: Combines both public and private clouds, providing flexibility and scalability.
3. Current Security Risks in2025
As cloud storage matures, so do the methods employed by cybercriminals. Organizations face a myriad of security risks that can jeopardize their data integrity, confidentiality, and availability.
3.1 Data Breaches
Data breaches remain a significant concern, with sensitive information often targeted. Cybercriminals exploit vulnerabilities in cloud applications or use phishing tactics to gain unauthorized access. In 2025, the average cost of a data breach has skyrocketed, making prevention paramount.
3.2 Ransomware Attacks
Ransomware attacks have evolved, with attackers targeting cloud storage directly. In these scenarios, malicious software encrypts files in the cloud, demanding a ransom for decryption. Organizations must implement robust backup solutions and incident response plans to mitigate this risk.
3.3 Insider Threats
Insider threats, whether malicious or accidental, pose considerable risks to cloud environments. Employees may inadvertently expose sensitive data, or malicious insiders might exploit their access for personal gain. Continuous monitoring and employee training are essential to address this vulnerability.
3.4 Misconfiguration
Misconfiguration of cloud settings is one of the leading causes of data exposure. Organizations often overlook the nuances of cloud security settings, leading to insecure data storage. Regular audits and adherence to best practices can help prevent these vulnerabilities.
4. Vulnerabilities in Cloud Storage
-
APIs: Application Programming Interfaces (APIs) are critical for cloud services, but they can also be a weak link in security. Poorly designed or insecure APIs can expose sensitive data.
-
Shadow IT: Employees may use unauthorized cloud services, leading to data being stored outside the organization’s control. This practice increases the risk of data breaches.
-
Inadequate Encryption: If cloud data is not adequately encrypted, it can be exposed during transfer or storage. This vulnerability can lead to unauthorized access and data theft.
-
Account Hijacking: Cybercriminals often use phishing or social engineering techniques to gain access to cloud accounts. Once inside, they can manipulate or steal data.
5. Best Practices for Secure Cloud Storage
Securing cloud storage requires a multi-faceted approach. Below are key best practices to enhance your security posture.
5.1 Encryption
Data-at-Rest and Data-in-Transit: Always encrypt sensitive data both at rest and in transit. Use advanced encryption algorithms such as AES-256 for data-at-rest and TLS for data-in-transit.
End-to-End Encryption: Consider implementing end-to-end encryption to ensure that data is encrypted before it leaves the user’s device and remains encrypted until it reaches the intended recipient.
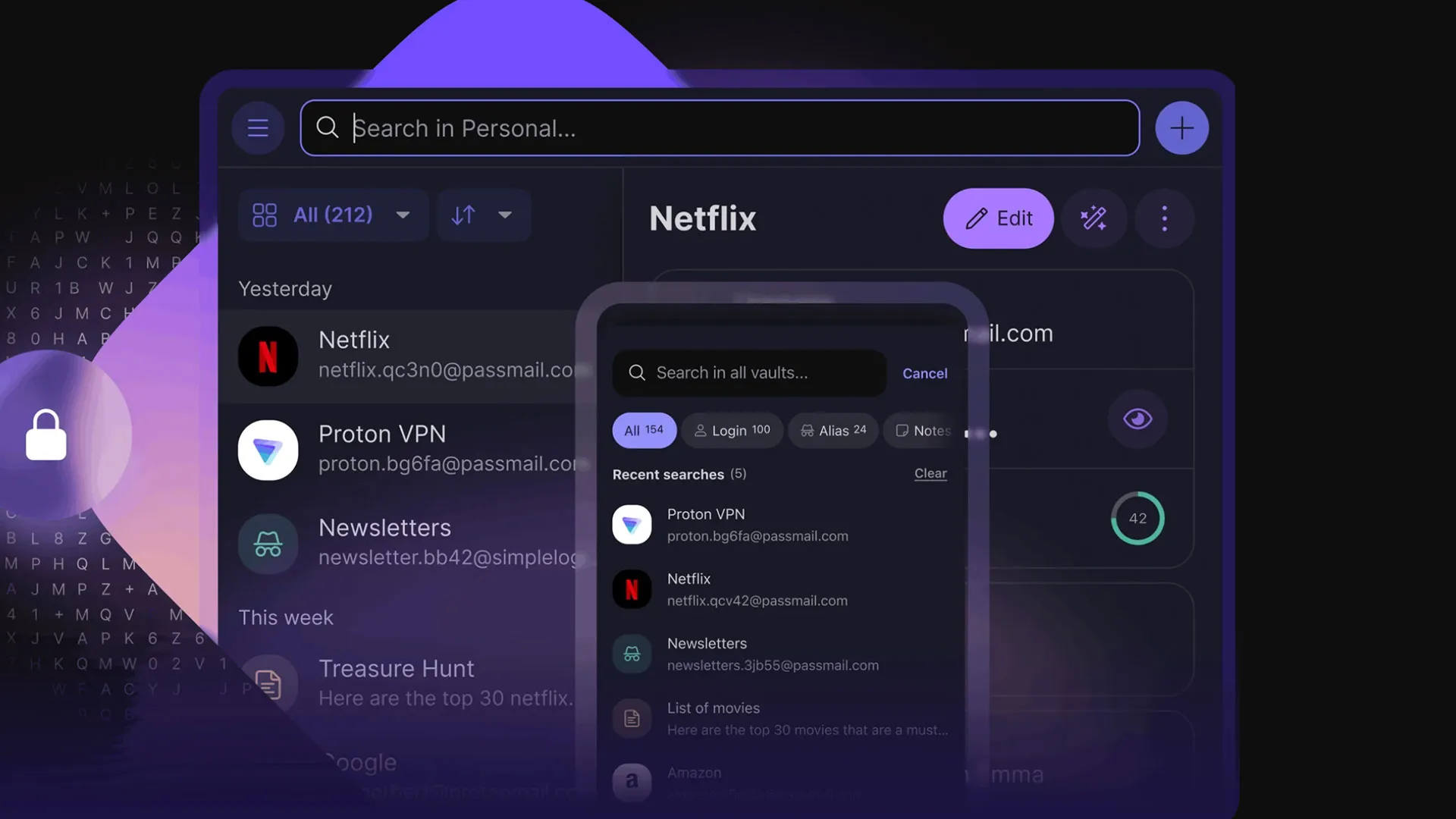
5.2 Authentication
Multi-Factor Authentication (MFA): Enforce MFA to add an extra layer of security. This could include a combination of passwords, security questions, and biometric factors.
Identity and Access Management (IAM): Implement IAM solutions to control user access based on role and necessity. Regularly review and update access permissions.
5.3 Compliance with Privacy Laws
Be aware of the legal landscape around data privacy. Regulations such as GDPR, HIPAA, and CCPA mandate specific security measures. Ensure cloud service providers comply with relevant laws.
5.4 Malware Protection
Utilize advanced threat detection tools that monitor for malware and anomalous behavior. Regularly update antivirus and anti-malware solutions to protect against evolving threats.
5.5 Threat Prevention
Regular Audits: Conduct regular security audits and vulnerability assessments to identify weaknesses in your cloud storage solutions.
Incident Response Plan: Develop a robust incident response plan to address potential security breaches swiftly and effectively.
6. Step-by-Step Instructions for Securing Cloud Storage
Step 1: Assess Your Requirements
- Determine what data will be stored in the cloud and classify its sensitivity.
- Identify compliance requirements relevant to your industry.
Step 2: Choose a Secure Cloud Provider
- Research cloud providers with robust security certifications (ISO 27001, SOC 2).
- Review their encryption standards, user management features, and incident response capabilities.
Step 3: Implement Strong Authentication Practices
- Set up MFA for all user accounts.
- Regularly cycle passwords and enforce strong password policies.
Step 4: Encrypt Data
- Configure encryption settings in the cloud storage service.
- Ensure that all sensitive data is encrypted before uploading to the cloud.
Step 5: Regularly Audit Access and Permissions
- Conduct quarterly reviews of user access and permissions.
- Remove access for users who no longer need it.
Step 6: Monitor for Threats
- Use security information and event management (SIEM) tools to monitor for security incidents.
- Set up alerts for unusual access patterns or unauthorized changes.
Step 7: Develop a Backup Strategy
- Implement regular backups of all critical data.
- Store backups in a separate, secure location.
Step 8: Educate Employees
- Conduct regular training sessions on cybersecurity best practices.
- Simulate phishing attacks to educate employees about recognizing threats.
7. Case Studies
Case Study 1: ABC Corp’s Data Breach
In early 2025, ABC Corp experienced a data breach due to misconfigured cloud storage settings. Confidential customer data was exposed, leading to a loss of customer trust and a hefty fine for failing to comply with GDPR. In response, ABC Corp implemented a comprehensive security strategy, including regular audits and employee training, significantly reducing their risk of future breaches.
Case Study 2: XYZ Tech’s Ransomware Attack
XYZ Tech fell victim to a ransomware attack that encrypted critical data stored in the cloud. By quickly implementing their incident response plan, they restored data from recent backups and mitigated losses. This incident underscored the importance of having a solid backup strategy in place.
8. Expert Insights
Expert Opinion: Dr. Jane Doe, Cybersecurity Researcher
“Organizations need to adopt a holistic approach to cloud security. It’s not just about technology but also about people and processes. Continuous education and proactive threat detection are key to minimizing risks.”
Expert Opinion: John Smith, Cloud Security Consultant
“Misconfiguration is often the weakest link in cloud security. Regular audits and compliance checks can significantly reduce the risk of data exposure.”
9. Conclusion
As cloud storage continues to evolve in 2025, the importance of security cannot be overstated. Organizations must remain vigilant, adopting best practices such as encryption, robust authentication, compliance with privacy laws, and threat prevention measures. By taking a proactive approach and fostering a culture of security awareness, businesses can mitigate risks and protect their valuable data in the cloud.
In a world where cyber threats are increasingly sophisticated, staying informed and prepared is the best defense. By following this comprehensive guide, organizations can enhance their security posture and confidently harness the benefits of cloud storage.